Instructure says data exposed in a hack of its Canvas software last week, which included thousands of WA students, is safe after it reached an "agreement" with the group behind the attack.
The company behind the Canvas education software, which was hacked last week exposing the data of millions of students, says all data is safe after it reached an "agreement" with the group behind the attack.
Canvas, a learning management system operated by Instructure, was breached on Friday with those allegedly responsible claiming to have exfiltrated some 3.65 terabytes of data impacting approximately 275 million individuals.
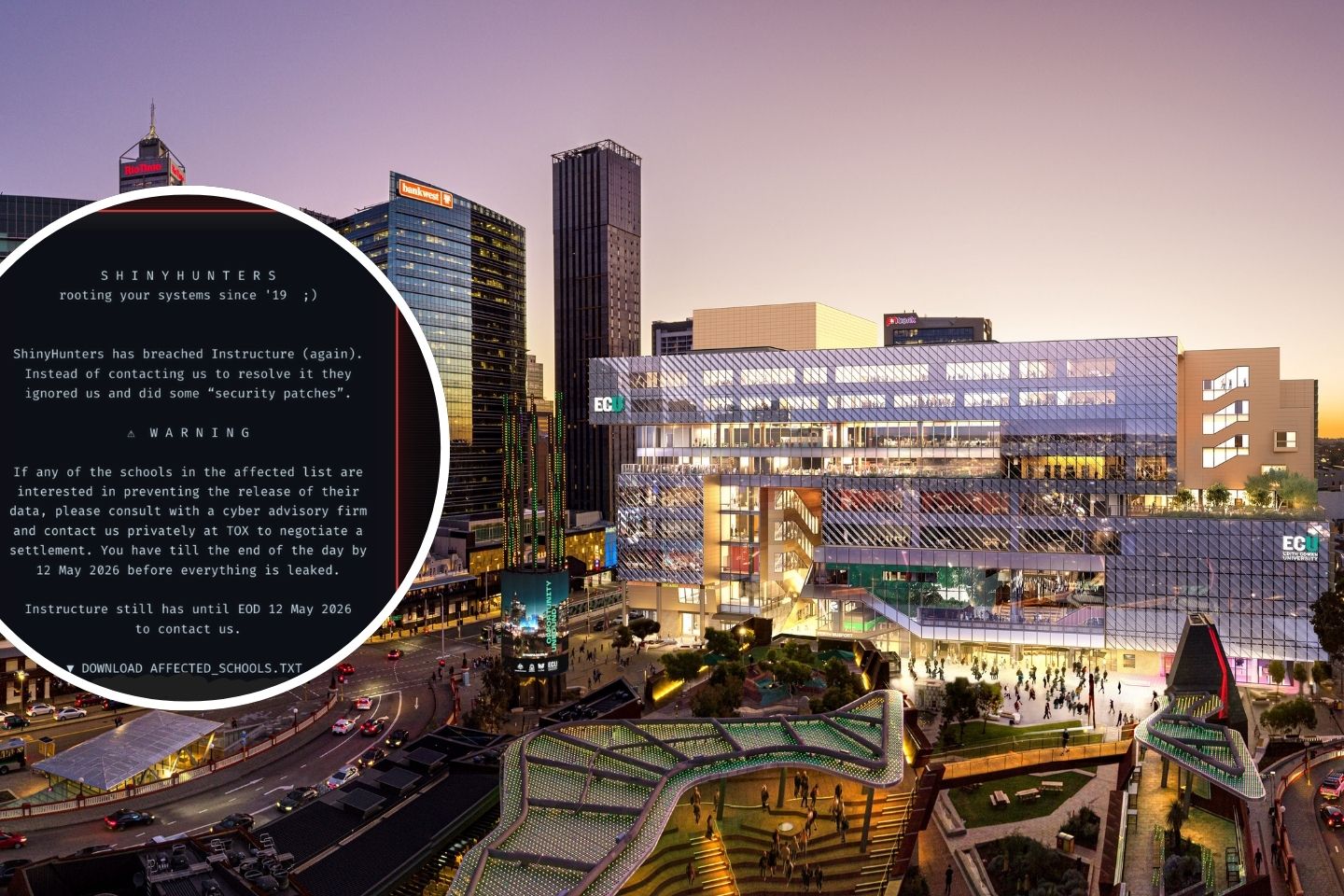
ECU and Curtin University were among 9,000 institutions globally to be impacted in the breach, which also included Harvard, Stanford and Apple.
The attack was claimed by notorious cyber-criminal group ShinyHunters; the same group which had previously claimed responsibility for the May 2024 hack of Ticketmaster and are believed to be part of a group responsible for last year's Qantas breach.
Data stolen in the breach included names, email addresses, student ID numbers and messages.
Instructure said last week no passwords, government IDs, birth dates, or financial data were stolen.
And in an update posted to its website overnight, Instructure said it had "reached an agreement" to ensure the data was not used maliciously.
"We know that concerns about the potential publication of data related to this incident remain top of mind for many customers. We understand how unsettling situations like this can be, and protecting our community remains our top priority," Instructure chief executive Steve Daly said.
"With that responsibility in mind, Instructure reached an agreement with the unauthorized actor involved in this incident.
"As part of that agreement: the data was returned to us; we received digital confirmation of data destruction (shred logs); we have been informed that no Instructure customers will be extorted as a result of this incident, publicly or otherwise; this agreement covers all impacted Instructure customers, and there is no need for indivudal customers to attempt to engage with the unauthorised actor.
"While there is never complete certainty when dealing with cyber criminals, we believe it was important to take every step within our control to give customers additional peace of mind, to the extent possible."
That statement followed an apology by the company earlier in the week, which admitted its communication on the breach had been sub-optimal.
"Last week, we made a call to get the facts right before speaking publicly. That instinct isn't wrong, but we got the balance wrong," Mr Daly said.
"We focused on fact-finding and went quiet when you needed consistent updates. You've been clear about that, and it's fair feedback. We will change that moving forward.
"Rebuilding trust takes time. We're going to earn it back through consistent action and honest communication. We're in this for you and your community."
Business News last week revealed ECU was among the impacted institutions after seeing an email from Vice Chancellor Braden Hill to students.
"We are aware that students are now experiencing access issues to Canvas," Prof Hill said.
"We understand this may affect your ability to access learning materials, announcements, classes and assessments. Please be assured that the University is working urgently to understand the impact and put support arrangements in place.
"You will not be disadvantaged because of Canvas access issues outside your control.
"We are working hard to understand the impacts on you, how we will address them and will provide further updates as soon as more information is available."
A ransom note from ShinyHunters last week, seen by Business News, claimed Instructure ignored their attempts to contact the company.
"ShinyHunters has breached Instructure (again). Instead of contacting us to resolve it they ignored us and did some "security patches"," the note said.
"If any of the schools in the affected list are interested in preventing the release of their data, please consult with a cyber advisory firm and contact us privately... to negotiate a settlement. You have till (sic) the end of the day by 12 May 2026 before everything is leaked."
Curtin University was also understood to be in the middle of a transition to Canvas; but it had not yet become the university's default learning management system, and therefore had not been as heavily impacted.
Curtin was contacted for comment.
In a statement following the breach, the Office of the Australian Information Commissioner said it was aware of the breach.
"Education providers, including universities, vocational providers and some state schools in Australia, have been affected," the statement said.
"The National Office of Cyber Security is coordinating the response."
The Commissioner's statement also flagged that only some organisations on the breach were covered by Federal laws.
"It is important to note that not all educational institutions are covered by the Privacy Act 1988. State and territory government schools are usually governed by state privacy laws, and public universities and TAFEs are generally exempt unless they operate as private entities," the statement said.
Under federal law, if a "serious harm" breach occurs, the institution must notify the person impacted.
This would cover private schools, universities and federal agencies.
State schools and TAFEs however, would be covered by state law.
WA's Privacy and Responsible Information Sharing Act, which cover state departments and institutions, is currently in a transition phase, with the right to be notified if personal information was involved in a breach not coming into effect until January 1, 2027.














